Do you know what are the common symptoms of stress? Most individuals are suffering from an emotional mind state(mental health), getting nervous which leads the […]
Beginner’s Guide to Investing in [Specific Investment Vehicle]
Investing is one of the challenging and complex concepts for most individuals concerning personal finance. It is always known as one of the prominent cornerstones […]
Creative Ways to Save Money on Groceries
In this modern era of economy, a single penny has a valuable amount. Most people are looking towards various creative ways to safeguard their hard-earned […]
The Rise of Plant-Based Eating: Benefits and Tips – Plant-Based Foods List
Are you looking for complete guidelines for plant-based eating, its benefits, and how to start the same in your daily life? Then, in this blog, […]
How to Live Zero Waste on a Budget – what is zero-based budgeting
Are you looking for effective tips and proper planning to achieve living a zero-waste lifestyle? In this article, we will be exploring the real meaning […]
Meds on Trial: 4 Drugs and Their Side Effect Debates
Prescription medications play a pivotal role in healthcare, often providing relief and improved quality of life for countless individuals. However, behind the curtain of therapeutic […]
Best Methods for Exam Preparation in Distance MA in English Programs: Tips and Techniques for 2024
In the constantly changing field of higher education, pursuing a Distance MA in English is an excellent endeavor. People can shape their academic fate thanks […]
Fraud Prevention in the Digital Age: Safeguarding Your Business Against Financial Threats
Today’s business landscape is as challenging as it is competitive. Companies have access to many business tools to help them conduct business more efficiently and […]
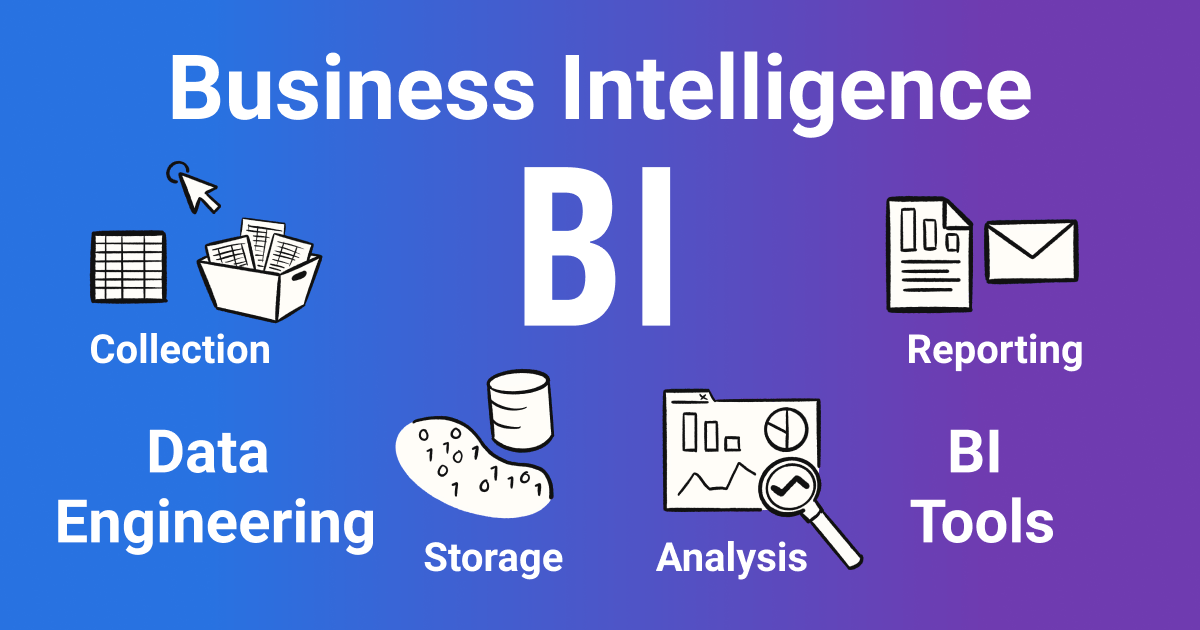
Business Intelligence and Analytics Market Growth Prospects
Business Intelligence or BI consists of the technologies and strategies used to analyze data. BI is also used for the management of information which is […]
Crypto and the Entrepreneurial Spirit: How Digital Currency Is Changing the Game for Startups
Image Source Digital currency, also known as cryptocurrency, is changing the game for startups, providing opportunities for entrepreneurs to access funding, streamline operations, and innovate […]

![Beginner’s Guide to Investing in [Specific Investment Vehicle]](https://allnewsstory.com/wp-content/uploads/2024/04/Beginners-Guide-to-Investing.webp)